Enabling Entra ID Security Mode
GENESIS security can synchronize with Microsoft Entra ID (formerly called Azure Active Directory).
When using Entra ID mode, you can optionally enable web login for Entra ID, allowing you to use single sign on and features such as multi-factor authentication.
This example requires the following prerequisites:
- Basic knowledge of GENESIS security and Workbench
- Microsoft Active Directory and Entra ID
- A public origin that is correctly configured Learn more
To enable Entra ID mode and configure web login:
-
Set up Entra ID, then get your Application (client) ID, Directory (tenant) ID , client secret, and initial administrator account.  Learn how
Learn how
 These settings may change over time. See Microsoft's documentation if you are having trouble following these steps.
These settings may change over time. See Microsoft's documentation if you are having trouble following these steps.
- Register your application on the Azure portal. More information about the registration process can be found here:
https://docs.microsoft.com/en-us/graph/auth-v2-service
-
Under API permission, add two new permissions:
- Microsoft Graph > Application Permission > Directory > User.Read.All
- Microsoft Graph > Application Permission > Directory > GroupMember.Read.All.
- Grant the application at least one Delegated API permission, either User.Read or openid.
- Select Grant admin consent for directory name. This step is necessary and requires administrative privileges to the Microsoft Entra ID.
- If you want users to be able to use the standard GENESIS login dialog, go to Authentication and enable
Treat application as a public client.
-
Note the following information:
|
Application (client) ID
|
App Registration > your app > Overview under Active Directory
|
|
Directory (tenant) ID
|
App Registration > your app > Overview under
Active Directory
|
|
Client secret
|
App Registration > your app > Certificates & Secrets > New client secret
|
|
Initial administrator account
|
Name under Owners > Username
 The initial administrator account name should be in the format of user@domainname.onmicrosoft.com for internal domain
users, and in the format of user_domainname.com#EXT#@domainname.onmicrosoft.com for external users. The initial administrator account name should be in the format of user@domainname.onmicrosoft.com for internal domain
users, and in the format of user_domainname.com#EXT#@domainname.onmicrosoft.com for external users.
|
-
Optional: Set security to testing mode to help keep you from getting locked out if something is configured incorrectly later.  Learn how
Learn how
 Do not make this change on a production system.
Do not make this change on a production system.
- In Workbench, go to Security > Global Settings > General tab.
- Set Security active to Testing.
- Apply the changes.
- Set the GENESIS security mode to Entra ID and fill the information from step 1.
 Learn how
Learn how- In Workbench, go to Security > Global Settings > General tab.
- Set Security mode to Entra ID
- Using the information from step 1, fill the Entra ID Settings section.
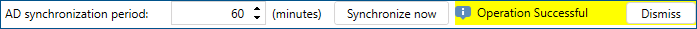
Select Synchronize now. After a moment, Operation Successful appears next to the button.  View image
View image
- Apply the changes, then open a login dialog and test logging into security with a Microsoft Entra ID user.
- Optional: Enable web login for Entra ID.
 Learn how
Learn howIn Workbench, go to Security > Global Settings, make the following changes, then click Apply.
General tab | Allow simultaneous login | Unchecked | |
Web Login tab > General Settings section | Enabled | Checked | |
Web Login tab > Authentication section | Type | Entra ID | |
Web Login tab > General Settings section | In-house applications use web login | Checked | Optional. Checking this will make applications such as Workbench and GraphWorX use the Microsoft login dialog. |
General tab | Automatic login | Unchecked | Uncheck this if you checked In-house applications use web login. |
- In the Azure portal go to Active Directory > App Registration > your app > Authentication and set OIDC URI to: https://GENESIS-server-name/fwxserverweb/security/signin-oidc
- Test logging into Workbench (if in-house web login is enabled) or a WebHMI display.
- If all tests succeeded, set security to active mode.
 Learn how
Learn how- In Workbench, go to Security > Global Settings > General tab.
- Set Security active to Active.
- Apply the changes.
 Learn how
Learn how Learn how
Learn how Do not make this change on a production system.
Do not make this change on a production system. Learn how
Learn how Learn how
Learn how Learn how
Learn how These settings may change over time. See Microsoft's documentation if you are having trouble following these steps.
These settings may change over time. See Microsoft's documentation if you are having trouble following these steps.